Serious cyber attacks and incidents – the kind that have serious long-term consequences - are, thankfully, relatively rare in most state and local governments. That said, they’re not nearly as uncommon as would be ideal and, perhaps more problematically, they seem to be becoming more common. So how do these jurisdictions prepare for such events? Planning, preparedness, and “cyber hygiene” efforts are all valuable, but an important part of the toolkit for learning how to do those tasks more effectively, and for testing existing practices, is through the use of exercises and simulations.
These exercises and simulations range in complexity from simple discussion-based exercises involving a small number of stakeholders to vast full-scale exercises involving live “play,” red teams, and multi-jurisdictional (or even multi-national) stakeholders. Some are tabletop exercises while others are full-scale operational exercises. Some exercise network defenders and their technical skills, while some focus on first responders who might deal with the second order effects of a cyber calamity, while still others engage state or local government executives to flesh out the response of leadership to potential attack scenarios. The variations are almost endless.
In order to think systematically about these exercises, one of the tools at our disposal is classification, meaning the use of typologies and taxonomies. Recently Spain’s cyber security agency published an excellent and valuable document: their Cyber Exercises Taxonomy. INCIBE was kind enough to translate it into English, but it is also available in Spanish. It is a very valuable and useful document. The taxonomy breaks down the kinds of cyber exercises that exist along several axes – including “focus” (the incident/roles being analyzed), “model” (the structure of the exercises), “vertical sector” (the industry or industries it focuses on), “scope of participation” (who the participants are), and “dissemination of results” (whether the findings are for internal or external consumption).
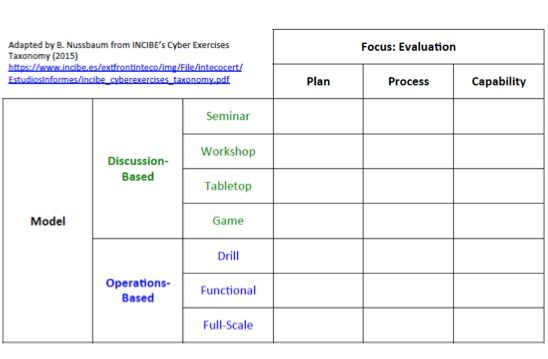
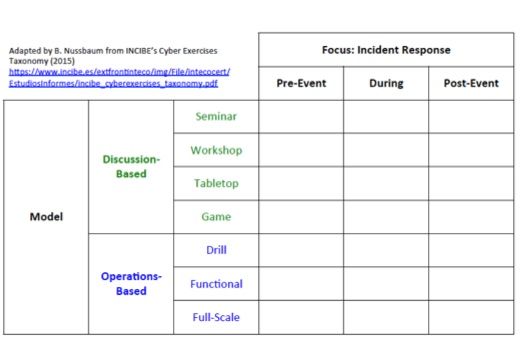
All of these are interesting, but the “focus” and “model” characteristics are particularly useful for breaking up the kinds of exercises that any particular set of stakeholders (like state and local governments) might be likely to engage in. If applying the taxonomy to state and local government cyber exercises, it is easy to imagine matrices of potential exercise types, like those focusing on evaluation or incident response:
Similar matrices could be used to examine other elements of the taxonomy (i.e. putting “scope of participation” on one axis, or examining “dissemination of results.”) Once such matrices were constructed, it would be interesting to see whether there were in fact evidence that such exercises were being conducted, which types are most common, which ones are less frequent, and then beginning to think about why. It is certainly possible that the distribution of different types of exercises could be driven by resource constraints, limited need or low threat levels, lack of clear lines of responsibility, or various other influencing factors.
Even a cursory examination suggests that there is much interesting activity to analyze using this kind of taxonomy. A brief search turns up fascinating and valuable state and local government cyber exercises - of numerous types and with various stakeholders involved - happening across the United States:
- Starting in 2004 the state of Delaware began an annual cyber security and continuity of operations exercise, which in 2014 celebrated its tenth anniversary. The exercises have morphed and changed over time, for example 2009’s event featured a tabletop exercise, whereas the 2011 and 2012 versions were a more complex series of linked exercises involving both business managers and technical participants from numerous local governments. The events were sponsored by CIAS, the Delaware League of Local Governments and by the Delaware Department of Technology and Information.
- Kansas has made public the scenarios it used for a 2009 continuity of operations (COOP) exercise it conducted related to cyber attacks. The scenarios, designed for cities and other local governments, describe a series of hacking attacks with serious consequences for businesses and local government operations. The document also features discussion questions to help local officials work through the scenarios.
- In 2014, around San Francisco, dozens of agencies, organizations and companies took part in a San Francisco Bay Area Cyber Tabletop Exercise sponsored by the Department of Homeland Security (DHS), the Northern California Regional Intelligence Center (NCRIC), and the San Francisco Police Department.
- The Huntsville, Alabama area conducted a joint cyber exercise with state (Alabama Homeland Security), local (Huntsville-Madison County Emergency Management Agency) and non-governmental partners (“Cyber Huntsville”) as sponsors, and with participants from the federal government, industry, and academia. The daylong tabletop exercise was focused on process issues rather than technical ones, and focused on cross-sector information sharing, as well as infrastructure interdependencies.
- In 2014 the New York Independent System Operators (NYISO) hosted the New York State Critical Infrastructure Cybersecurity Exercise sponsored by the Department of Energy. It featured 120 participants from “13 electric and gas utilities, industry organizations” which is to be expected, but they also note that “federal, state, local, tribal and neighboring territorial government entities participated.” According to the Executive Vice President of NYISO, the exercises demonstrated needs have led to plans to form a New York State Security Working Group with both utilities and government partners.
- In its 2015 Cyber Initiative, Michigan lists “increase number of cyber security exercises” as one of its goals, and claims it will conduct annual state level exercises during the next four years. Michigan also lists many previous exercises – ranging in scale and scope - in its timeline of cyber security accomplishments. Notably, they mention an “executive-level cyber tabletop exercise” designed to ensure state leaders are involved in such exercises, rather than just those focused on information technology professionals.
- Hawai’i is about to begin the 2015 Po’oihe (or roughly “tip of the spear”) cyber security exercise looking at the cyber impacts of a potential hurricane strike on the state. The exercise is sponsored by the State of Hawai’i National Guard, the state Information Technology Services Department, and by the University of Hawai’i at Manoa.
There is very good work going on in these states and localities. It will be interesting to see these efforts mature, to watch best practices emerge, and to see the spread of thoughtful cyber preparedness.
